While it’s the longest-running joke in the world of IT, the question “Have you tried turning it on and off again?” is still an important one to consider when things are going awry. There’s a good reason why it’s such well-known advice, too: turning your device off can help solve a significant amount of technical issues. Why is this the case, and what can you learn from it?
SMART Blog
Over time, you might add new technology solutions to your infrastructure to solve specific problems. Before you know it, you might have an overwhelming amount of technology that keeps your business operational. This issue—tech sprawl—can hold your business back from efficient operations, but don’t worry… we have a solution for you.
We’ve all heard it, perhaps even rolled our eyes at it: “Have you tried turning it off and on again?” This seemingly simplistic question has become a running gag in the world of IT support. But beneath the humor lies a fundamental truth: rebooting a device is often the most effective first step in resolving a surprising number of technical glitches.
We understand that, although it might sound elementary, this advice is based on solid technical principles.
The world of cybersecurity is in constant flux, demanding that organizations continually reassess their defensive strategies. A traditional focus solely on preventing breaches, while important, is proving insufficient in the face of sophisticated and persistent threats. As highlighted in a recent Illumio podcast episode, "Trust & Resilience: The New Frontlines of Cybersecurity," the very foundation of digital interaction—trust—has ironically become a primary vulnerability exploited by attackers. This necessitates a fundamental shift in perspective.
If you're like many small and medium-sized business owners, you're juggling countless online passwords… for email, banking, software, supplier portals, and more. It's overwhelming! This often leads to using simple or repeated passwords, which unfortunately opens the door to cyber threats like data breaches, a serious risk for any business. Thankfully, there's a straightforward solution: a password manager.
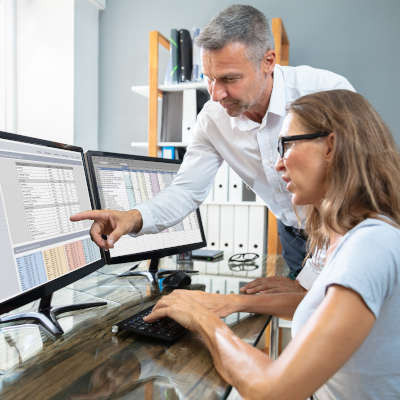
Small businesses today generate a lot of data. From customer details and sales records to inventory tracking and employee schedules, you need to be able to structure this data so that you can use it effectively. Keeping that data organized and accessible is important, but managing it effectively can often be a hassle. This is where smart database management comes in. When done right, it helps businesses run smoother and often save money.
Bring Your Own Device, or BYOD, is a common approach for businesses that want to take advantage of mobile technology to kickstart productivity. Instead of supplying each individual employee with company-owned devices, businesses allow employees to use their own devices for work-related purposes. While this is great on the budget, it’s only really effective (and safe) if the employee prioritizes security on their devices; otherwise, it’s a liability.
The Android operating system periodically receives updates and patches detailed in online publications called Android Security Bulletins. In the March 2025 edition, Google announced that 43 malicious bugs had been resolved, two of which were zero-day vulnerabilities.
Let’s talk about how to implement these fixes and why this is a practice that should reach every aspect of your business’ IT.
It should come as no surprise that cybersecurity is a big challenge for businesses and individuals alike. The problem: life pretty much revolves around being online these days, so there’s no avoiding it. Therefore, it’s your responsibility to ensure that any data you collect from your customers, employees, and other key stakeholders in your business is well-protected, otherwise you will face severe consequences.
In the United States, tax season is prime time for hackers to take advantage of law-abiding, tax-paying citizens. They do this through all kinds of nefarious activities, such as phishing attacks conducted through text messages and emails claiming to be from the Internal Revenue Service. If you want to avoid getting scammed this tax season, be sure to keep the following tips in mind to stay safe while you conduct your typical tax routines.
Hardware is far from the most fun topic for a business owner to learn more about, but that doesn’t diminish its importance. If you want to ensure your business stays ahead of the game, then you need to be strategic about your hardware implementation. Otherwise, you risk falling behind, put your business in danger, and—even worse—imperil your budget. Today, we want to help you get the most out of your hardware, long before you have to invest in anything new.
If you want your business to succeed, you need to take care of your employees, but businesses sometimes let this important task slip in the throes of the day-to-day. Deloitte estimates that around 8 out of every 10 wage workers show signs of burnout. So the question then becomes… What are you doing about it?
If they are doing their job well, a business’ decision makers are always looking for ways to increase efficiency. For years, businesses were looking to their human resources to improve, but today, technology can fill in the gaps more effectively. A culture of automation--the act of having machines do tasks that humans used to do--is proving to be a potent strategy for all types of tasks.
It’s a safe assumption that your business relies on some technology in order to operate (after all, you are reading a blog on the Internet). As a result, it is likely that you will require some level of IT support at some point. While this may sound like something simple enough to find, you need to keep in mind that not all IT service providers will necessarily provide the same quality of service.
COVID-19, or coronavirus, has been a major global health concern over the past couple of months. At this point, it is clear that this disease could have serious impacts on the workplace. We wanted to provide a brief rundown of good workplace and network health practices, as well as a few pointers on how you can handle health-based employee absences.
The way people talk about cybersecurity, it’s as if it is something like a television or a new phone: something you can just buy. That’s not the truth. When you are seriously looking at how you can keep unwanted entities off your network, while having control over what you do with your technology, you need to look at it as three levels of security.
Many states’ stay-at-home orders that are/were designed to mitigate the spread of the COVID-19 virus are now lapsing all over the U.S. As a result, business owners are re-opening their doors to a great deal of uncertainty. We have put together this guide to help the business owner understand that, even though you’ve finally been given the go-ahead, you have a responsibility to keep your staff and customers safe.
A business without well-trained employees is one that is always on the precipice of disaster. With the threat landscape the way it is, you need your staff to know how to properly maneuver around company IT and you need to ensure they know how to protect themselves and the company in a digital environment. Today, we will take a look at some strategies to promote end-to-end security at your company.