Running a small or medium-sized business means juggling countless priorities. You're focused on your customers, team, and bottom line… but what about the technology that powers it all?
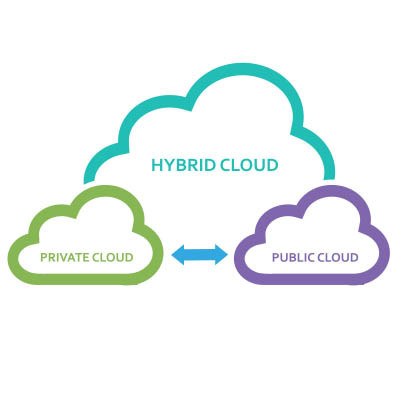
Often overlooked, your IT infrastructure is far more than just the computers on desks. It's the complex web of network equipment, essential software subscriptions, cloud services, and even the personal smartphones and tablets your employees use for work. Keeping this entire ecosystem running smoothly and securely is a significant challenge for many SMBs.