SMART Blog
Phishing is the most common way hackers “get you”, but have you ever wondered why it’s so effective? Today, we want to explore the reasons why phishing schemes are so enticing to even the most security-conscious individuals out there. You might be surprised to know that even security professionals can fall prey to these types of attacks, and for very good reasons.
Your business needs software, along with the various integrations it allows for to keep your operations going. A little planning goes a long way, especially if you want to get the best return on your investment. Today, we want to look at how you can find the right mix of software for your business without breaking the bank or experiencing the dreaded “tech sprawl.”
Every business’ worst nightmare is a data loss incident, and if you’re caught unawares, such an incident can set you back financially and operationally for months. Today, we want to cover some of the common data your business collects that you absolutely need to have backed up. If you don’t, you could become subject to serious fines due to regulations and other industry-specific mandates.
As you should be aware by this point, the Windows 10 operating system is reaching its end of support on October 15 of this year—meaning that it will no longer receive updates of any kind afterward, including critical security updates. What you may not know, however, is that Microsoft is following suit and pulling Office support around the same time.
At the beginning of this year, a massive data breach struck a location data broker called Gravy Analytics and took possession of a dataset with 30 million points from devices worldwide. This data could potentially be used to track individuals and their movements, tellingly, through healthcare, government, and military facilities.
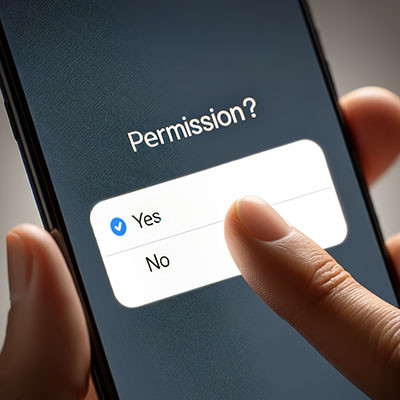
Unfortunately, nothing can be done about data that has already been breached, but preventative steps can and should be taken to protect your business. Let’s discuss how to prevent your applications from tracking your movements.
Unless you’ve been living off the land in the wilderness for the past couple of decades, you’ve heard of Facebook, Twitter (now X), and Instagram. Most people have some type of social media presence on one or all of these platforms (or at least on LinkedIn, TikTok, or YouTube). Many businesses once used or currently use these platforms as a part of their marketing efforts, and despite being billion-dollar companies, there are some serious concerns about the viability of these platforms going forward. In this week’s blog, we will discuss some of the problems people are having with these established social media platforms and how alternatives might just be the future of social media.
Did you know that phishing is, by far, the most common security risk to your business? Just think, any of your employees could become the target of a phishing attack, and all it would take is downloading the wrong file or clicking on the wrong link to expose your organization to security threats. Today, we want to offer a refresher on the throwaway signs of a phishing attack and how to protect yourself and your team from harm.
Net neutrality has long been an embattled topic, with rules flipping every few years depending on the opinions of those with influence. Recently, the Federal Communications Commission had its most recent net neutrality policy struck down by the 6th Circuit Court of Appeals… in such a way that sets the concept back to square one.
Let’s discuss why this is a particularly dangerous decision, and very well could put small and medium-sized businesses at a distinct disadvantage moving forward.
For years, the telephone has been one of the most tried-and-true business communications solutions, and that trend will continue into 2025. If you’re still using the phone solutions of the past, however, you’ve got some upgrading to do. Here’s what you need to know about the best communications investment you can make: Voice over Internet Protocol, or VoIP.
Many market analysts and industry experts foresee an increase in the cost of hardware. We recommend that you take matters into your own hands to dodge the price hike and purchase your new IT now before it costs you more to do so. The implementation of any proposed tariffs could impact the market as early as February 2025, so we wanted to discuss what you should consider when purchasing new hardware today.
If you want more productivity from the workday, then multiple monitors can help you achieve this goal. You might run into the issue of “ghost monitors,” though, where your PC believes you are connected to screens when you’re not. If you experience this issue and your application windows are off-screen and unobtainable, you’ll find this week’s tip helpful.
With the price of hardware at risk of skyrocketing, it’s no wonder that many businesses are looking to virtualize as much of their operations as they can. This is where the cloud comes in; you can virtualize just about any solution, including some that you might not have considered in the past. Let’s explore how an SMB might use virtualization and cloud computing to skirt hardware acquisition costs.
Do you ever feel at home in your business’ server room? That is, assuming you have a server room, and it’s more than just a stuffy closet in an isolated part of your office. If you’re not confident that you can provide your servers with the management, maintenance, and monitoring they need, we recommend you work with a managed IT company to ensure you get the most value you can from your server units.
Your Android device offers a lot of capabilities in its little frame, with many people relying on theirs to keep their lives organized and generally handled. Many businesses even rely on Android mobile devices. This should only reinforce how critical privacy and security are.
In light of this, we’ve shared a few simple tips anyone can do to help make a smartphone that much more secure.
There is a concept known as the iron triangle that provides a simple framework for project management by outlining the balance between your costs, your available time, and the desired quality of your outcome.
Traditionally, the iron triangle helps illustrate how these factors impact each other. Instead, we wanted to take advantage of the principles of the triangle to explore how beneficial it can be to outsource IT services.
Since so much of the world is now online, businesses and organizations interact with people online now more than ever. This means they also collect people’s information, a practice they do for various reasons. Individuals need to consider their own data privacy and how it might be affected by business practices.
The big thing in business computing is AI, or artificial intelligence, and businesses are implementing it to solve a lot of repetitive problems that free up their employees to serve other roles. One such area is for IT support. But is it worth it to chat with a robot when something as important as IT is on the line?
While we all know how much magic the workshops up at the North Pole rely on to produce presents for the good children of the world, we have it on good authority that they also rely on quite a bit of technology. For instance, there are a lot of letters that need to be sorted and read before Santa’s big ride. Let’s read up on what our partners up north frequently deal with in their critical operations.