SMART Blog
The modern workplace wouldn’t exist as it does without the advent of wireless Internet or Wi-Fi. Understanding how your wireless router works can be incredibly helpful for any business owner, and it can help you get even more out of your wireless connection. Today, we want to share some information about wireless routers that can help you use them more effectively.
If you could generate more revenue without spending more, wouldn’t you?
If you share most people's goals and aspirations, the answer is a resounding and enthusiastic “yes.” Scaling a business is an important element of continued success—provided it is carried out correctly. Let’s discuss how you can help ensure your success, partly by implementing the right technology.
For any business to succeed, it needs to exhibit some degree of empathy toward its audience. Otherwise, the services and products they offer will be less likely to meet the priorities and needs that its targets are experiencing.
As a managed service provider, this is perhaps most true of us, as our services revolve around predicting the needs of our clientele and resolving them… ideally, before the client even realizes they have a need to fulfill.
Any business can benefit from data and use it to improve its operations. This is especially the case where information technology is involved. By collecting the right metrics, you can better evaluate your business IT’s performance and identify areas for improvement.
Let’s review what some of these metrics should be.
Mobile malware isn’t common, but it’s growing increasingly more so. You may have heard of a malware called XLoader, which has been used to victimize people in over seven countries. This mobile threat has seen various iterations over the past several years, but you should be especially concerned these days.
How important do you consider security for your personal and private data on your web-connected accounts? If you don’t think about it often, you should be; countless entities out there—including major enterprises and providers you trust—do not respect your data privacy and security. Let’s discuss how some large companies take advantage of your data and some of the questions you should consider when trusting these companies with your data.
Software is an important part of any business’ toolset, and for small businesses, Software as a Service, or SaaS, is the most cost-effective way to take advantage of it. The most profitable companies in the world run on SaaS, and so too can your business. Let’s go over some of the most powerful solutions your organization can implement in the realm of software and how they can benefit your success.
We could go on and on about the benefits of using Voice over Internet Protocol (also known as VoIP) for your business telephone needs. However, it is important that you do everything you can to prepare your network for this kind of utilization. Let’s review a few tips to help make sure your network is properly optimized for VoIP.
PDF, which stands for Portable Document Format, is a type of file that business professionals are all too familiar with. While most are aware of and appreciative of this file type, they likely are not aware of some of the more fun and useful features afforded to them. Let’s explore just what PDFs are capable of, including how to make and edit them.
From smartphones to laptops and everything in between, our devices are constantly exposed to dirt, dust, and germs. Keeping your technology clean ensures a longer lifespan for your devices and promotes a user’s health. Today, we'll explore four practical tips to help you keep your technology clean and functioning at its best.
Video conferencing has really taken off in recent years, due in no small part to the COVID-19 pandemic, which forced remote work on most businesses worldwide. However, businesses see the benefits of video conferencing, and it has now cemented itself as a go-to communications solution for all businesses. Today, we want to discuss how to make virtual meetings and video conferencing more productive and more engaging.
It’s easy to look at a power strip and a surge protector and question if there’s anything that actually makes them different. After all, they both give you extra plugs, right?
Yes, but there’s more to it than just that. Let’s review some of the important differences between the two that make one a far better choice for your business’ power delivery needs.
SMBs need to be able to navigate the complexities of IT, whether it’s with a completely outsourced IT department or an in-house team of technicians. However, if you are thinking of technology management in this black-and-white way, you are eliminating the potential for enormous benefit through the use of co-managed IT.
For the IT administrator and the small business owner, it can be a bewildering experience when your company comes under siege from employee-induced cyberthreats; especially if you, like many other companies, have started prioritizing security training. Even if the threat is thwarted early and the effect on the business is negligible, it is important that you trust the people who have access to your organization’s digital resources. Let’s look at some of the reasons some of your staff take cybersecurity initiatives worse than others.
Businesses will often go into the process of self-improvement with unrealistic expectations for how much they can significantly improve their functionality. This simply is not true, and sometimes business owners need to realize that real change—the kind that yields real results—takes time. Thankfully, there are some actionable steps you can take to ensure that your business is moving in the right direction.
Technology can bring a lot of value for businesses, but sometimes it can be difficult to nail down exactly what can make a business run optimally. There are a lot of options, but all that means is that there are a lot of things that can potentially go wrong. Let’s take a look at some of the technology that small businesses are using to support the new workplace and create better opportunities.
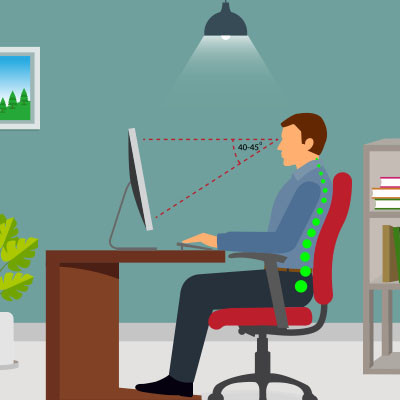
The strain on people’s bodies isn’t always taken seriously when someone works at a computer. Still, many official studies suggest that desk jobs can have a radical and rather negative effect on the health of individuals. One common ailment is what is called “tech neck.” Tech neck is a term that describes neck pain and damage stemming from looking down at computers or mobile devices for prolonged periods. To avoid tech neck, you can follow these helpful tips.