SMART Blog
Two-Factor Authentication Frequently Asked Questions
Data security is such a core consideration of the modern business that every small effort you can take to protect your business is important. One such effort is the implementation of two-factor authentication. However, your employees may not initially feel entirely comfortable with some facets of two-factor authentication.
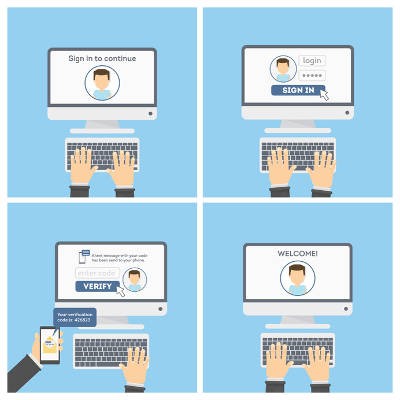
The two-factor authentication platform adds a valuable layer of security to your existing solutions by requiring an additional credential beyond just your typical username and password. This can be a PIN that is generated by an application or even a physical token like a key fob that provides access.
To make a long story short, your employees may not feel entirely comfortable with your organization requiring them to keep an application on their phone as they may value the autonomy they have over what they do and don’t keep on their personal device. As a result, they are bound to have questions that you will need to answer.
To assist you with this, we’ve compiled a few questions you may have to field, and how to answer them truthfully and diplomatically if you choose to implement two-factor authentication for your business.
What is it?
Two-factor authentication is another way to improve data security and prevent threats from infiltrating business network’s access points. Picture your network as a house that your data lives in, with the front door being the access point. The lock on your doorknob is your usual access credentials, username and password. 2FA adds a deadbolt to that door.
In other words, 2FA is the added security that can keep many threats out, at the cost of a tiny bit of convenience.
Why do I have to do this?
This line of questioning is indicative that an employee is resistant to change--unfortunately, information technology is built on change. Threats to a business’ security are always improving so they have the best chance of creating the most impact. To counter this, a business must acknowledge the risks inherent in powerful technology platforms and do everything they can to control access to their network. 2FA is just one of many ways to do that.
It is also important to remember that a chain is only as strong as its weakest link, so the entire business could be made vulnerable if one person doesn’t have the same dedication to organizational network security as the rest of the team. By implementing 2FA as a team, the business is better protected by the team.
Why do I have to do it on my personal phone?
This answer has two parts to it, one in the best interest to the business, the other being for the employee’s benefit. First off, economics. Does your business have the capital to spare to distribute mobile devices for the singular purpose of enacting 2FA? Typically, this isn’t the case.
Furthermore, which device is an employee more likely to favor? Their personal device that they have conditioned themselves into bringing everywhere, or the new, unfamiliar device they were just given for work?
What happens if I lose or forget my phone?
There are ways to get around a forgotten or misplaced device. In many cases, an organization can adjust an employee’s 2FA settings to allow them access via a new 2FA code, but this will require the employee to change their credentials. If the phone is lost, the company is still safe, as the Mobile Device Management platform that the 2FA implementation was likely part of will allow network administrators the requisite authority to handle the situation.
Can you see my personal stuff?
This question will likely come up. You should ensure your employees that the privacy of their personal data will not be betrayed, and that the authenticator will only be used to access their company materials.
Information can be a touchy subject, and its security is of paramount importance. Reach out to us at SMART Services for more help with your company’s data security.
Let Smart Services position your agency for tomorrow’s technological challenges. For more than 25 years, Smart Services has helped agencies across the U.S. face a changing environment by providing innovative technology solutions that allow agencies to focus on growing their business. MyAgency Cloud, our complete cloud solution, covers all your technology needs in the cloud or at your agency. In today’s competitive environment, it’s time to make your agency technology a strategic asset, instead of a liability. Let us show you how. To learn more, please call our expert agency technology advisor at 586-258-0650.




Comments