Google Workspace is a great tool that allows you to get a lot done, but sometimes you might find yourself in a position where you need to download the files and take them with you or send them to someone. In these cases, you might not want to share the link. Instead, you can simply download them as whatever file format you might need!
SMART Blog
Data breaches—any event where a business’ confidential data is viewed, copied, or stolen by an unauthorized person or party—are a serious problem. Unfortunately, they are also a serious problem that can be caused by no shortage of situations. Let’s review some of the causes of business data breaches so you’ll know what to keep an eye out for.
The telephone has been a part of business processes since it was invented, with businesses quickly taking advantage of the new features that telephony has introduced as it has improved over the years. VoIP—Voice over Internet Protocol—is the latest improvement, and as such, offers businesses a lot of great benefits to embrace.
Tomorrow, March 31st, is the official World Backup Day, a day intended to remind us all of the importance of taking backups for the sake of data continuity. While this kind of day can be a valuable reminder of a critical best practice, we contend that your awareness of your backup (and the associated maintenance of it) should not be limited to a single day.
Passwords have been a primary data security measure since 1960, when MIT researcher Fernando Corbató suggested the practice—although even he is reportedly slow to take full credit. Why? Well, if you ask Corbató (and his contemporaries, who were the first to implement passwords as we’d recognize them today), the security concerns were limited.
So, have we reached the point where it would be best to replace passwords as the default authentication measure?
One of the great obstacles many businesses have to remote work is the fact that, well, the team will be remote—not in the office, safely under supervision. This has led many to consider using the webcams installed in their employees’ devices to keep tabs on them. Let’s explore the idea of monitoring your team, and why it probably isn’t a good one.
The COVID-19 pandemic has shown us that not all companies have considered how to be flexible in their operations, but it has also given them opportunities to adjust accordingly. With these new flexibilities in place, what does the future of your office look like? Would you ever consider a hybrid approach to the workplace?
World Backup Day is March 31st, each and every year. However, while there is value to having a dedicated holiday to raise awareness of the need for backup, it should not be the only time it is considered. Let’s go over the importance of proper backup practices, just in time for the holiday, so that you can establish the backup that your business needs if it's not already in place.
The cloud is far and away one of the most beneficial technologies that a modern business has at its disposal. Unfortunately, the same can be said for modern cybercriminals. The cloud has given cybercriminals new opportunities that are important to acknowledge—as well, of course, to protect your business against.
Today is Global Recycling Day, and is intended to remind us of all the materials that can be reused in everyday life, in part as a way to decrease our individual carbon footprint. However, it's valuable to know how much your business contributes in terms of its carbon footprint… and, once you know that figure, how you can reduce it.
We’ve all seen our friends and family sharing quizzes on their social media profiles, prompting people to find out what their celebrity stage name or what Hogwarts house you would be in, or to share what their first concert experience was. These fun, lighthearted quizzes are a great way to get to know a little more about the people we’re connected with… and that’s the biggest problem.
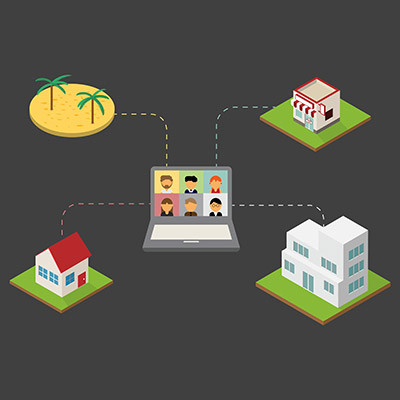
Today, remote workers are constantly asked to endure meetings over their organization’s chosen video conferencing applications and while it may not be an ideal situation to enhance the collaborative flow of your team, there are certain variables that you can control to get the most out of your company’s virtual meetings. Let’s take a look at a few:
Gauging the effectiveness of your cybersecurity can be a bit of a daunting task, especially when asking if it could make a major difference in protecting your organization’s network infrastructure. If you want to track and measure your business’ cybersecurity preparedness, here are four steps to help you perform an evaluation.
With so many great smartphones on the market, there are bound to be a couple that stand out for being innovative and interesting in their designs. These devices—many of which fall into the foldable category—are pretty neat and worth looking into. Here are some of the better options on the market today.
A lot of people like to venture predictions about what the future will bring for business, and many of those predictions are based on anecdotes and hopes. When it comes to information system management and the future of IT for business, there are a lot of claims made by companies looking to take advantage of the reliance on IT and present business owners’ and decision makers’ options on how to leverage this technology for their own good. Today, we thought we would take a look at three emerging technologies that we will all come to use in the future and whether they are right for your business now.
Collaboration is not just nice, it is the only way many businesses can afford to keep the lights on. Understanding that truth makes it important to find the right strategies and technologies to support your staff’s collaborative endeavors. Today, we take a look at a few options to help improve your business’ collaboration.
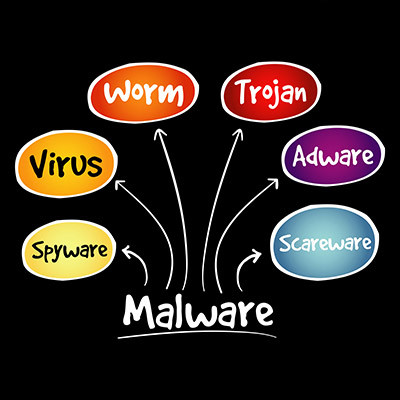
Network security could mean any number of things, but more often than not, people are using the term as a blanket statement against the dreaded idea of malware and its many forms. Today, we are discussing how vast the world of malware can be and how often you might find yourself misunderstanding what it exactly is. Knowing all this can help you identify if you have become a malware victim or not.
Microsoft has planned an increase in the price of its software offerings Microsoft 365 and Office 365, and make no mistake, it will impact your business in some way whether you are ready or not. We are writing this blog to share information that you might find important about this price increase so you can plan to get the most out of your software moving forward.